Git authentication failed
If you’re using HTTPS token authentication and receive a “Git authentication failed” error, this typically indicates an issue with your access token. Common causes include:- Expired token - Access tokens have expiration dates. Check if your token has expired and create a new one if needed.
- Insufficient permissions - Verify that your token has the required permissions:
- For GitHub: Contents (read and write), Metadata (read-only), and Pull requests (read and write)
- For GitLab:
api,read_repository, andwrite_repositoryscopes
- Incorrect token format - Ensure you’ve copied the entire token without any extra spaces or characters.
- Token revoked - The token may have been revoked in your git provider. Generate a new token and update it in Omni’s git settings.
- Verify your token is still valid and has the correct permissions in your git provider.
- If needed, generate a new token with the appropriate permissions.
- Update the token in Omni by navigating to Model > Git settings and clicking the Change Token button.
Git push failed
GitHub
If you are receiving the following error: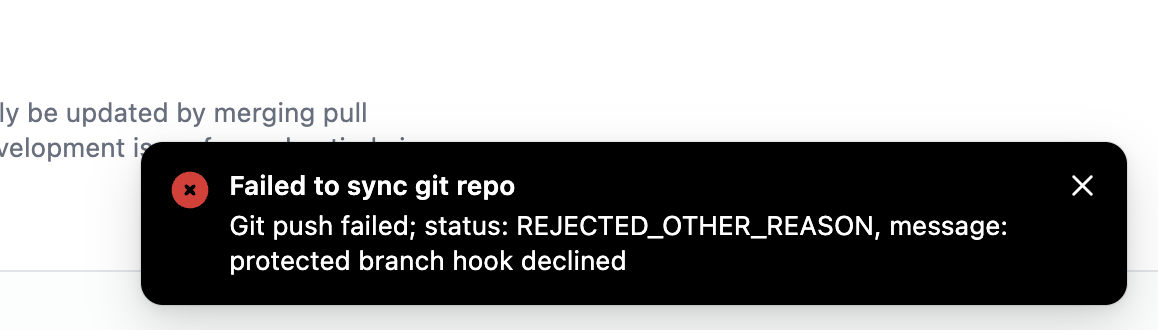
- Omni has to be able to force push schema changes, but approval is required for pull requests made by users.
- Require Omni to go through the pull request process for all schema refreshes by turning on Require system syncs as in the screenshot below.
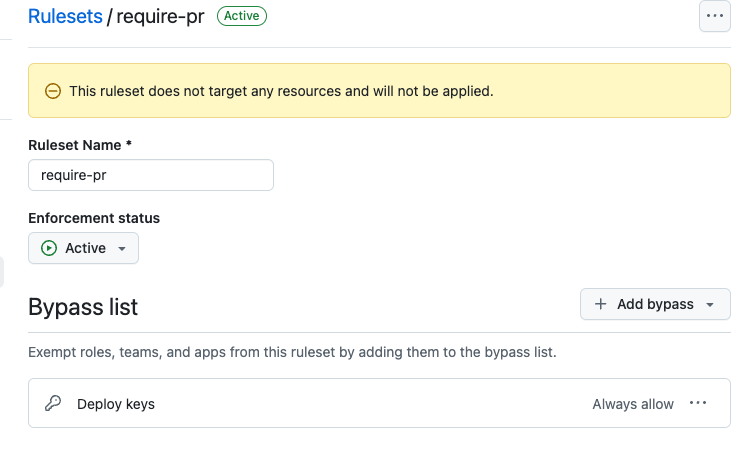
Option 1: Allow schema refreshes to bypass pull-requests
- In the git settings for your shared model, set the
Require pull requesttoggle to true. - In the git repo’s settings, add a GitHub ruleset to require pull requests. Select the rules
Require pull request before merging,Block force pushes, andRestrict Deletions. - On the same ruleset’s settings, add a bypass to the bypass list.
Option 2: Require pull requests for all changes
- In the connection settings for your model, enable the
Branch Based Schemas Refreshsetting. - In the git settings for your shared model, set the
Require pull requestand theRequire for system syncssetting.
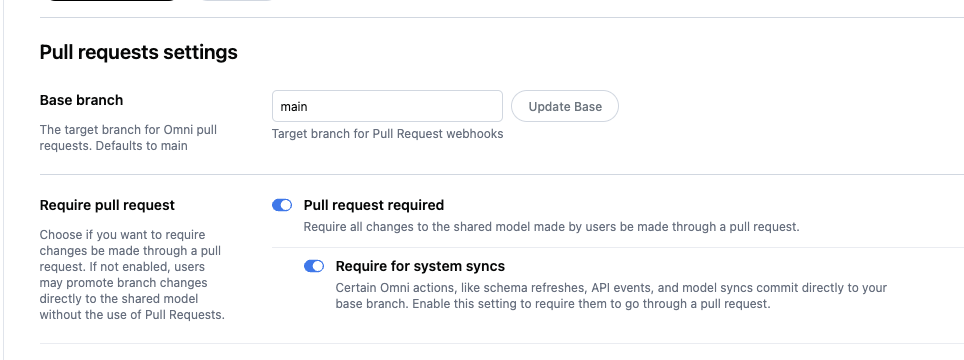
- In the git repo’s settings, add a GitHub ruleset to require pull requests. Select the rules
Require pull request before merging,Block force pushes, andRestrict Deletions. Do not add anything to the bypass list.
Webhook secret compromised or expired
Webhook secret rotation is only available when using SSH authentication. HTTPS token authentication does not use webhook secrets.
- Security incident - Your webhook secret was exposed in logs, code, or leaked in a security breach
- Suspected unauthorized access - You suspect someone has accessed your webhook secret
- Routine security practice - Regular credential rotation as part of your security policy
- Provider notification - Your git provider (such as GitHub) notified you that webhook secrets may have been compromised

